For most people, technology is like a car – they just want to use it, they don't want to be an engineer.
 CradlePoint PHS300 Per...
Best Price: $19.99
Buy New $71.99
(as of 05:00 UTC - Details)
CradlePoint PHS300 Per...
Best Price: $19.99
Buy New $71.99
(as of 05:00 UTC - Details)
Here, I'm going to cherry pick the easiest and most useful ways I know to communicate and use the internet privately. My earlier article "Practical Internet Privacy" was pretty low-tech; this one is as close to no-tech as possible.
Techies might quibble, but useable low to medium strength privacy is better than none. Also, the "security through obscurity" factor should not be dismissed – who is going to spend hours hacking your difficult but not impregnable email?
But I will also add some easy but optional extra strength privacy tips where relevant.
Anything from your home broadband carries with it the internet equivalent of Caller Line ID, so one privacy key is to make use of the many open, free Wi-Fi "hotspots." Or, along with a disposable prepaid SIM card, you can even have your own mobile Wi-Fi hotspot (alt.). There is some info at the end on how to use your home internet privately.
Easy Voice Call Privacy
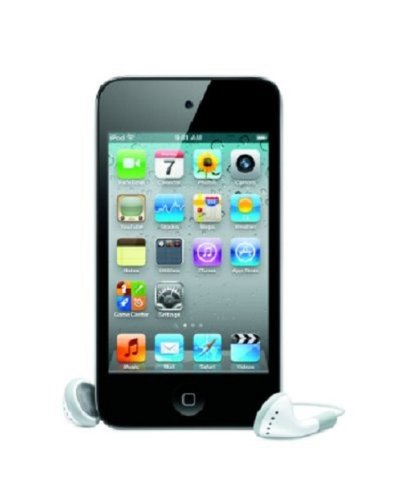 Apple iPod touch 8 GB ...
Check Amazon for Pricing.
Apple iPod touch 8 GB ...
Check Amazon for Pricing.
For easy call privacy get an iPod Touch, the brand new model is just over $200 and has a built in microphone – optional earphones with remote and mic are under $20.
Then, choose one or both of these apps:
-
With the free Skype app, you can call other Skype users privately and with "SkypeOut" credit, call regular numbers. But first, set up a new Skype username – preferably not from your home internet. Luxembourg-based Skype may or may not be able to piggyback a username to monitor calls, but otherwise your call is private.
-
The "Acrobits Softphone" app is about $10 at the iTunes store ("Bria" is a good app too).
With this, you can make and receive regular phone calls, but you will also need an internet phone account – the voice equivalent of an email provider (try Link2Voip). You can then make outgoing calls, but a regular "Direct Inward Dial" (DID) phone number is usually an optional extra – or try a free IPKall number to start.
Instead of an iPod Touch, iPhone or iPad, you could also use a laptop and headset. To do this, both Mac and Windows users can install the free Zoiper Classic "soft-phone" and/or Skype.
Or, want something private but zero-tech for Skype only? Get an Ipevo Skype Wi-Fi phone, just punch in your new Skype username and sit in a quiet corner of any internet cafe.
Extra Strength Privacy Tips:
- Create a new iTunes account and register the iPod Touch anonymously by using iTunes vouchers
- Use generic personal info when signing up
- Sign up to the call provider using a money order
- Buy SkypeOut credit privately using PayByCash.com.
Easy Document Privacy
This is really easy, in just three or four clicks. First, you need to pre-share a password with the recipient, and then all you need is a secure "file archiving" program.
For Windows, first install the free program 7-Zip. Then just right click on a document: Move the cursor to "7-Zip," click "Add to Archive," choose Archive Format>Zip and under Encryption enter your password – or just follow this easy video tutorial. Clicking OK will create a very secure, password protected "zip" file.
For Windows recipients only, choosing "7z" for the archive format and ticking "Create SFX Archive" will create a self contained file – so no unzip software is needed at the other end, just the password.
Mac users can also read and create secure zip archives by using BetterZip or the free CleanArchiver.
Extra Strength Privacy Tip: Choose "AES-256" encryption type – impregnable but less compatible.
Easy Email Privacy
One way to privately pre-share a password by email is to use the answer to a question you both know, but others would not.
You could then just email one of the above secure zipped documents as an attachment – but in order to stay completely off the record, use what is called an email "dead drop":
First create a new free webmail account, preferably with a secure email provider in another country. (Try Mailvault, Hushmail, PrivacyHarbor).
Then, instead of sending an email, you can both access the same email address – saving drafts or editing the same draft. A new password can be suggested at any time, for the other person on their next login to implement. When the email/draft exchange is over, the last one out deletes everything.
Extra Strength Privacy Tips:
- Password protected documents can also be transferred as attachments via an email dead drop.
- Some webmail services can list previous login details, to easily spot an intruder.
 Zoom 4506 3G Wireless-...
Best Price: $49.95
Buy New $58.99
(as of 07:30 UTC - Details)
Zoom 4506 3G Wireless-...
Best Price: $49.95
Buy New $58.99
(as of 07:30 UTC - Details)
Easy Surfing Privacy
Airports, military bases and other public internet facilities often spy on users and/or block websites – especially hotbeds of dissent like LewRockwell.com.
One easy way round this is to use a website translation service like Bing Translator. By translating both from English and to English, the target site is fully accessible, but only the translator's web address is visited. For example, here is LRC.
Easy Online Shopping Privacy
Just create a new Amazon account using widely available Amazon Gift Vouchers and personal info of your choice – only, make sure the physical address works…. and don't look surprised when the delivery guy asks for John Smith…
Easy Home Internet Privacy
The idea is simple – a bit like making a telephone call to your work switchboard from home and having them call a third party and then patching you through.
Your home phone bill shows only a call to the switchboard; the third party caller ID shows only a call coming from the switchboard; the switchboard phone bill shows only a call to the third party. To mix it up further, lots of others are using the switchboard at the same time.
A "VPN" (Virtual Private Network) is a private internet switchboard – you stay invisible because all your activity goes through this, making you appear to be coming from the VPN location.
On an iPhone, iPad, or iPod Touch there's no need even to install software, as it's already built in. On a regular computer, the VPN provider's instructions will make it easy.
You will need to pay for a subscription. Try Perfect-Privacy – they are tried and trusted, have servers all over the world, keep no logs, and the service will work with the iTouch/iPhone/iPad as well as computers. Or, try Cryptohippie with their businesslike customer service – though for regular computers only.
Extra Strength Privacy Tip: Just like getting a phone number from directory enquiries, the internet has what is called a "Domain Name System" (DNS). Choose a VPN service that has a solution to the "DNS leaks" that can reveal sites you visit on Windows, Linux and sometimes Mac computers.
Final Thoughts:
Using either a public Wi-Fi hotspot or a VPN service means you won't leave a trail to your door when using the internet.
Every once in a while, to illustrate a point in answer to a privacy question, I have taken a couple of minutes to ID an email sender. They are usually shocked when I tell them their workplace, their home address and their age, as well as their friends and interests. It doesn't even require special tools, just an internet search starting with the unique home internet number or "IP address" embedded in their email.
So bloggers, dissenters, whistleblowers, offshore accountholders – beware, and get some easy internet privacy.
September 6, 2010





