Survival Saturday is a round-up of the week’s news and resources for folks who are interested in being prepared.
This Week in the News
Cyber-criminals are no longer just striking huge targets. They’re going after average people like you and me now.
Never have our personal electronic devices been under more threat. From apps that steal your money to ransomware that locks up your computer to a flaw in Bluetooth devices that allows anything connected to be hacked – including your car – every person using a cell phone or a computer is vulnerable.
Many of us use our devices to conduct business, like banking, bill-paying, or shopping. In fact, these days, it’s increasingly difficult to function if you don’t. I’m not suggesting we all need to get rid of our phones and computers, but we might want to be a lot more careful than we have been in the past,
We’re used to reading about cyber attacks and hacks affecting large businesses or power grids, but things are getting a lot closer to home. Like, actually in your home. These 4 stories about threats to our personal devices all took place over the past few weeks. Being prepared isn’t just about beans, bullets, and band-aids. It’s about knowing what the risks are in all aspects of your life. If you’re reading this, you are on a device that probably has the potential to be hacked, so read on for information on the current threats.
Buy Silver at Discounted Prices
For regular updates on the world of preparedness, be sure to sign up for my daily newsletter.
First, your Bluetooth handsfree safety feature isn’t that safe.
Cell phones can be a great way to communicate with loved ones, but don’t underestimate the dangers lurking within all their “conveniences.” I wrote a story that went largely unnoticed last week about a flaw with Bluetooth that allows any device connected to easily be hacked. To summarize:
- BlueBorne is an attack vector that could affect billions of devices.
- If you’re running IoS, Android, Windows, and even Linux, your devices could be at risk.
- This makes all of your connected devices vulnerable to cyber espionage, data theft, and ransomware.
- If your passwords are saved for your bank or credit accounts, you can be easily hacked due to this vulnerability.
- Anything on your devices is under the control of the hackers.
But perhaps even worse than your phone being under control of the hackers is that this attack vector is “contagious.” Anything your device is connected to is subject to the hackers. So, that means there is the possibility that while you safely use your phone hands-free while driving, your car could be hacked…accelerator, brakes, heat, radio, lights…you get the idea.
It isn’t like this hasn’t been suspected to have been done before. Who can forget the death of journalist Michael Hastings? Blueborne takes this out of the realm of conspiracy theory and into the hands of any moderately skilled hacker. Get the details of the Bluetooth flaw here and see if you have any of the vulnerable devices. I did, and I disabled Bluetooth on my phone and laptop both.
Have You Downloaded Any of These Apps? They May Be Stealing Your Money
And while we’re talking about the dangers of your cell phone, SHTFplan reports that dozens of apps from the Google Play store have malware that can steal your sensitive data and drain your bank accounts. (Get the details here.)
The following apps have been downloaded millions of times and may contain the malware:
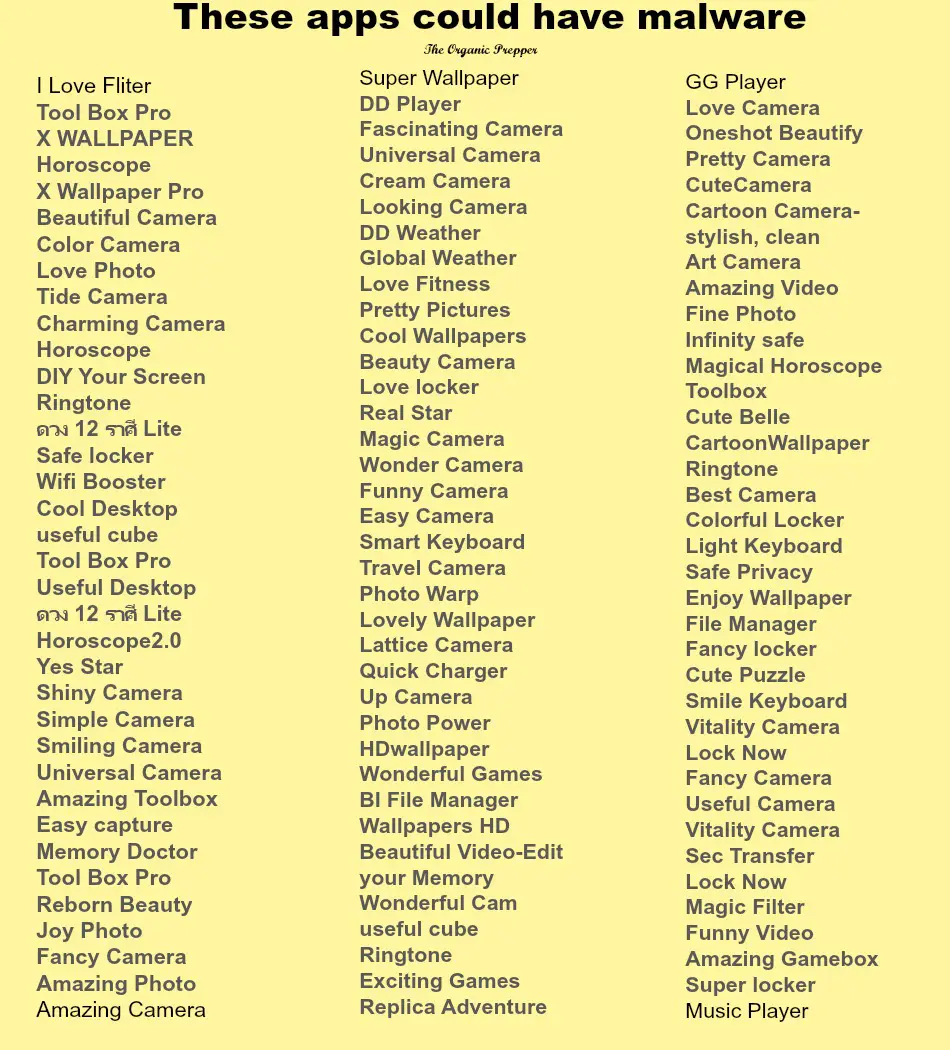
(List via SHTFplan)
If you have any of these apps on your phone, you need to completely remove them from your device immediately.
A massive ransomware attack is attacking millions of devices.
The attack is difficult to contain because it has 8000 different versions of the virus. Once one is stopped, there are 7999 to take its place. It’s attacking 2 million devices per hours. Here’s what Eugene Weiss, lead platform architect at Barracuda, says you should know:
- Automated hacking: “Nobody actually sat there and made 8,000 digital modifications,” Weiss said. The way they do it is by using a kit that essentially automates code variations.
- What to watch out for: An incoming email spoofing the destination host, with a subject about “Herbalife” or a “copier” file delivery. Two of the latest variants Barracuda has detected include a paragraph about legalese to make it seem official, or a line about how a “payment is attached,” which tricks you to click since, as Weiss puts it, “everyone wants a payment.”
- The hackers are using social engineering to get people to click. That’s increasingly becoming a trend, per Weiss. It’s “less pure technical hacks” and instead using psychological tactics “get someone to click on something they shouldn’t be.”
- If you remember one thing: “Don’t click the link, that is absolutely the most essential thing.“
- The targets: Email addresses at businesses or institutional groups in the U.S. or Canada.
- It’s likely not a nation-state perpetrating the hack, since the hackers’ motives are financial. Instead it’s a small, sophisticated group of criminals. (source)
Remember: “Don’t click the link…” Just don’t do it.
Oh, and while you’re trying to fix all these masses, hackers hid malware in a clean-up tool.
CCleaner, a tool to help speed up how fast your computer runs, has been infected with malware. The tool is made by software company Piriform, which is part of Avast, one of the largest computer security companies in the world. That makes it particularly embarrassing that the company got hacked and the hackers embedded malware into their computer clean-up tool.
The malware reportedly tried to connect to unregistered websites in order to remotely download even more harmful programs to users’ computers.
Security experts say the Trojan horse-style attack hackers launched affected over two million CCleaner customers who downloaded the product in August. (source)
Of course, this works because users already trust the company they’ve been successfully dealing with, so they download whatever is recommended.
Avast says that the problem has been resolved:
“Piriform believes that these users are safe now as its investigation indicates it was able to disarm the threat before it was able to do any harm.” (source)
A malware expert from Talos says that this is very similar to the attack on Ukrainian accounting software last June, the not-Petya attack without a kill switch that went global.
Talos researcher Craig Williams said it was a sophisticated attack because it penetrated an established and trusted supplier in a manner similar to June’s “NotPetya” attack on companies that downloaded infected Ukrainian accounting software.
“There is nothing a user could have noticed,” Williams said, noting that the optimization software had a proper digital certificate, which means that other computers automatically trust the program. (source)
The compromise was kept pretty quiet by Avast, but here’s what we know.
Piriform said that Avast, its new parent company, had uncovered the attacks on Sept. 12. A new, uncompromised version of CCleaner was released the same day and a clean version of CCleaner Cloud was released on Sept. 15, it said.
Only the cloud version could be updated automatically to remove the bad code.
The nature of the attack code suggests that the hacker won access to a machine used to create CCleaner, Williams said.
CCleaner does not update automatically, so those who installed the problematic version will need to delete it and install a fresh version, he said.
He also recommended running an antivirus scan.
Williams said that Talos detected the issue at an early stage, when the hackers appeared to be collecting information from infected machines, rather than forcing them to install new programs.
Piriform said in a news release that it had worked with U.S. law enforcement to shut down a server located in the United States to which traffic was set to be directed. (source)
I guess the moral of this story is, “Trust no one.”
This Week in Preparedness…
This month has been one of the worst for disasters that I’ve ever seen. As of last week, there were still 2 million acres burning in wildfires in the Western US. Hurricane Harvey destroyed 185,149 homes and my friend Lisa Bedford, the Survival Mom, told me there are still people living in tents in her suburban neighborhood, without plumbing or electricity.80% of the hurricane victims in Texas didn’t live in flood zones and did not have flood insurance. Hurricane Irma damaged or destroyed 90% of the homes in the Florida Keys. Between the two hurricanes, more than one million cars were damaged. The second of two massive earthquakes this month in Mexico left millions without power, destroyed buildings, and killed hundreds. Then there is the devastation in the Caribbean from two back-to-back Hurricanes, Irma and Maria. Entire islands have been destroyed and are barely habitable. Puerto Rico is completely without power and yesterday a major dam broke, causing even more devastation.
There are lessons from all this. Prepping with stuff is extremely important – just ask the folks living in homes without power for multiple weeks after these disasters how nice it is to have shelf-stable emergency food, an efficient way to cook it, and clean water how glad they are to have those things. But prepping with skills is even more essential.
If you lost absolutely everything…
- How would you eat?
- What would you do for shelter?
- How would you purify water?
If you can’t immediately answer those questions, you aren’t prepped, no matter how many supplies you have. Focus on doing and learning, not just buying.
Reprinted with permission from The Organic Prepper.




