There are lots of reasons you might prefer not to have every website you visit and email you send logged and recorded for years to come. I can't think of any why you would. In many countries, however, internet providers are required by law to do just that.
According to the London Telegraph, from April 2009 that now includes all European Union countries. For the tech-minded, here are the gory details. You can be sure it is being done elsewhere, legally or otherwise. For a global overview with "heat map," you can check out last year's "Electronic Police State" international rankings here. Surveillance is even more intense in large corporate or government environments, where you may also have trouble visiting certain "unapproved" sites.
At the other end of your internet connection, the same thing may be happening. Browsing and emailing, for example, usually discloses an "IP address" – the equivalent of your internet telephone number – which can be traced to you through your internet provider. Many sites, such as Google, also build up a profile of your activity based upon your IP address, "cookies" (data stored from earlier visits), search requests and other factors, which can be retained indefinitely. Forums and blogs will often record your IP address along with your comments and retain them for years.
This was underlined to me some time ago, when I had a problem with a Google search. In order to proceed, they required verification by typing in random letters, partially obscured in an image. After a couple of failed tries, on the third attempt Google presented me with a word consisting of my name complete with a spelling mistake peculiar to details held by my internet provider (a large multinational). At that moment, I was not using any privacy techniques. Nevertheless, I now have a new provider and often use the powerful, private Ixquick alongside Google.
Individual hackers can be a danger when they identify your IP address: A 17-year-old boy was recently jailed for what is known as "Swatting" his online-gaming opponents. According to The Register, on multiple occasions, he obtained their IP addresses and hacked their internet provider for their personal details. He then called in armed SWAT teams to their houses by faking ("spoofing") their telephone numbers in emergency calls.
You should note the low to non-existent standards of evidence under which the State will dispatch violent military force against the innocent. In fact, not only did the State effectively assist him, he was much less guilty when compared to the confiscation, tasering, torturing and killing of governments everywhere against their own opponents.
This highlights by far the biggest privacy concern: Accumulated profiling by Big Brother in order to identify dissenters, protesters, whistleblowers, tax escapees and political opponents.
But, there are fairly easy ways to keep "two sets of books" with your internet provider and also to "anonymize" your site visits, posts, chat, voice, video and email. It all starts with a clean computer:
Practical Privacy – Stage 1
Many PCs are riddled with viruses, spyware, toolbars, "helpers" and weighed down with bloated "security" suites. If you have a PC, then do what I have done for many hundreds of customers in recent years: First, get rid of Norton/Mcafee or similar bloat-ware and restart. Next run "msconfig" as in this tutorial (Vista users just type "msconfig" in the Search box). Restart.
The best and leanest antivirus is currently the free Avira Antivir. You will also need weekly or monthly manual scans with Spybot (un-tick all options except Desktop Icon on install). Do a scan with both and that's it. In case of a stubborn problem try a Malwarebytes one-off scan. If problems persist, then a backup and system reinstall is needed. Note that you don't need a complicated firewall because your router acts as a double hardware firewall, plus there is an adequate built-in Windows firewall anyway.
With a clean, fast computer the first and easiest privacy step is to clear it of data retained from previous activity. This can be available through the internet to others via things like cookies and add-ons like Java or Flash. You can clear it in this way:
On a PC, get the free CCleaner. Un-tick everything except Desktop and Start menu shortcuts on install. Ideally, run CCleaner just before and just after any private browsing is required. The standard settings are fine – except be sure everything is un-ticked under Options>Advanced. Expect the first run to take a while and to be surprised how much junk there was. After that it will usually be instant. For an equivalent, Mac users can use free programs like "Onyx" or "MacJanitor."
With this security setup and a little care about what you click on, you can have years of trouble-free computing, with the basics in place for some privacy.
Practical privacy – Stage 2
The next step is to obscure your activity from your internet provider, and to obscure your identity at sites you visit. There are several ways of doing this – most requiring technical knowledge of things like "proxies" and "shell accounts." But there are easier ways:
In an emergency, one obvious way is to drive around with a laptop and find a public or open internet connection. This would normally only reveal your general geographic location. If you are not doing anything to attract, for example, SWAT teams and are not hogging a lot of bandwidth, then you are harming no one. Long-range wireless is also an option.
One other way would be to use the TOR anonymous internet system. The only problem here is the unreliable browsing speed. It is quite easy to install and try, though.
For a permanent, reliable solution you need access to a Virtual Private Network or "VPN" service. VPNs are often used by businesses to securely log in to office networks from home. A VPN privacy service can completely obscure your IP address from sites you visit, while obscuring and encrypting the content, sites and servers you visit from your internet provider. Basically, it will tunnel everything you do to another computer in another part of the world of your choice. It does mean trusting the VPN provider to some degree (the best keep no logs) and it does mean paying a subscription. But you will get fast or even full internet speeds – in my own case, reliable enough to do chart-based day-trading.
Both Mac and Windows users can easily connect using the basic VPN software already built in. Or, there is a better solution called "OpenVPN." Versions of this on the Mac include "Viscosity" and Tunnelblick. The service provider will supply instructions.
One VPN service I use is Perfect-Privacy, with multiple servers around the world. I also like the very low-cost SwissVPN in Zurich. Bear in mind that lag will increase the further away you are from the VPN server. There are many others (metropipe, cryptohippie, xerobank, secretsline etc.).
One technical warning about "DNS leaks": These can bypass your VPN so that although actual content is secure, the names of sites visited could be visible and therefore logged. The fix does require extra steps but is reasonably easy: full instructions and a test here.
 Panasonic Black USB Sp...
Check Amazon for Pricing.
Panasonic Black USB Sp...
Check Amazon for Pricing.
Email Privacy
With a VPN setup, you can be less concerned about trusting email providers and using encryption. Just get a free web-based email address in another country and always use the VPN to access it. However, be careful not to include identifiable personal info in the email content.
In addition, for moderately sensitive email content, both sender and recipient could use temporary Hushmail accounts. Or, learn to use highly secure PGP encryption with any email provider. Other free options include Mailvault (with easy PGP built in) the secure (but US-based) Cryptomail, Privatdemail. Subscription options include Neomailbox and GeneralMail. However, unless you encrypt your own email, remember you are placing trust in an unknown service provider. Rumors abound, for example, that the popular Safe-Mail is a Mossad "honeypot" – though I have seen no real evidence of this.
Voice and Chat Privacy
Because a VPN connection is a secure tunnel (at least, from you to the VPN server) there can be less concern also with voice, video and chat services. However, here are some extra security steps:
For extra Instant Messaging security, try OTR. For voice and video content there is ZPhone (at both ends) in conjunction with Yahoo messenger or Apple iChat. Skype will conceal content from casual eavesdroppers, but many suspect a "backdoor" and your activity is logged by their software. Gizmo5 may be an alternative with its internal encryption, plus it will work with Zphone. SIP Communicator is a one-stop secure video/IM/chat solution with encryption (including ZPhone) built in.
But do be aware that unless you use a VPN, voice and email encryption only prevents wiretapping of content and does not prevent tracking who you are and who your contacts are.
Phone Privacy
For interaction with regular telephones you really need a "SIP" account – which is a bit like an email address for voice/video. These can also be assigned a regular phone number.
Get a free SIP account from IPTel, AntiSIP, SIP2SIP or PBXes. VoipUser will also give you a free incoming and outgoing UK telephone number. You can get a free US incoming number from IPKall. An incoming local number could be forwarded and used in conjunction with an "offshore" outgoing provider (e.g., Link2Voip, Switzernet, Peoplefone, Voipgate) for call records privacy.
Note that "IAX" is a better but less common alternative to the SIP standard (see IAXterminator, EuroIAX, Les.net, Voipgate).
The popular but US-based CallWithUs offers calls (only) via their own OpenVPN connection, as do Brujula. Link2Voip offer "IPSec" VPN access for calls, useable with some dedicated routers, from computer desktops, with the iPhone/iPod Touch, and with most Windows CE smart-phones and PDAs (IPaq, HTC etc).
If you do not have an incoming phone number for your SIP account, with some providers you can still be called using the free SipBroker service. This service has local numbers in many countries and you are contactable via an "extension" number after the local number has been dialed.
Making calls through a VPN does reduce the need for call encryption. But, on top of that, free software like Qutecom and MiniSIP have end-to-end encryption built in. SIP Communicator includes encryption not only for SIP calls, but also secure video/IM/chat. XLite does not include encryption, but is very popular and will work with Zphone. Also see Zoiper for both IAX and SIP.
In practical use, there is no need to be bound to computer speakers and microphone: you can easily use USB, wireless "Bluetooth" (inc. mobile phones) and other headsets or handsets.
A SIP account will also work without the need for a computer via special standalone "IP phones" or with regular telephones via SIP adapters. These plug in to your home broadband router. But if you want them to go through a VPN, there are then two options: You could set up "Internet Connection Sharing" on a dedicated computer with a VPN connection. Or (for the tech-minded only) here is the setup for a specially modified home router. For offices, the Draytek 2820 looks like a one-stop broadband/VPN/SIP solution.
Mobile Call Privacy
When on the move, Wi-Fi and SIP capable mobile phones, PDAs, or netbooks can offer more privacy than a regular landline or mobile call, even without a VPN connection. But it is possible to use a VPN through public wireless networks from many smart mobiles:
The iPhone and the iPod Touch offer an easy solution by including VPN software. The Apple app store offers SipPhone to make calls. Third-party offerings like Fring and Gizmo5 also work, but with less privacy and more lag (search for Youtube tutorials). You will need a microphone or hands-free set for the iPod Touch. "Jailbreaking" the iPhone/iPod Touch opens up other options, including Siphon – obtainable through the alternative "Cydia" download source. 2G iPod Touch models can easily be set free in less than 5 minutes, older models in less than a minute. You can be sure of a solution from the same sources after new updates.
The IPaq and other "Windows Mobile" phones and PDAs include VPN connection software. OpenVPN is also available for some. For making SIP phone calls, SJPhone is popular, PortSip is another.
Nokia or other "Symbian" models need SymVPN – also check that particular models have a SIP dialer inbuilt (e.g., Nokia E51).
But overall, a tiny netbook could be the stylish, all-in-one privacy option for home, office and on the move. For voice calls, it might be most convenient when used with a handset, or linked via Bluetooth (wireless) to a headset or mobile phone. You might consider the excellent Asus EeePC 1000HE with 9.5-hour battery life, or the popular Samsung NC10.
Payment Privacy
Of course, one big problem – and partly the reason I have suggested many free services – is a lack of internet payment privacy. This has strengthened the now pervasive custom of demanding personal, private information with every transaction. Here are some solutions to look at:
In the US, you could check out the various over-the-counter Mall Cards available. While in the UK and Europe, Paysafecard (e.g., for Amazon vouchers), UKash, and the Prime Card or Payzone prepaid debit cards are the nearest equivalents to cash online I have found. UnLinq is a worldwide (US-based) card option. There are also "virtual card" resellers with varying degrees of privacy. Debitcards4all currently have a good reputation at the talkgold forum, where you can also find other available options. For sending and receiving small payments, consider ePayarea.
You could also look at gold- or fiat-backed e-currencies. However, stability is a concern as is the intrusive information demanded by most exchangers – even if you pay in cash. Of all e-currencies, the soundest may be Pecunix. The most widely accepted – since the fall of e-gold – is probably the fiat-based Liberty Reserve.
For lightweight privacy, note that in many countries you can add an additional cardholder name to an existing card account.
Identity Privacy
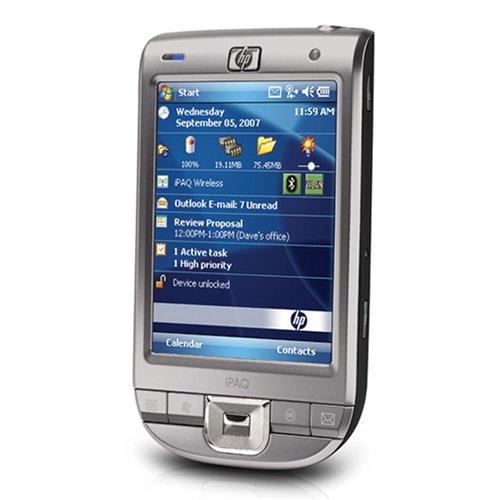 HP iPAQ 111 Classic Ha...
Best Price: $115.00
Buy New $248.41
(as of 12:05 UTC - Details)
HP iPAQ 111 Classic Ha...
Best Price: $115.00
Buy New $248.41
(as of 12:05 UTC - Details)
Under the present system, if you want to avoid identity theft, hacker attacks, profiling and more, you need to be cautious about giving out personal information:
Wherever possible, refuse, confuse or completely separate your name, address, date of birth and any other identifying numbers. Understand that you do not have a moral obligation to help a stranger track you against your will. Legally, at least in common law countries, you can call yourself whatever you like. I also do not recommend you supply, for example, your actual date of birth – just to open a free email account.
Some online privacy suggestions:
Always "enhance" your date of birth; If you must supply your name or, for a delivery, your home address, then not both together; Make use of junk email services like Mailinator or Dodgeit; If possible, don't register – use logins from bugmenot. Create throw-away email addresses for minor online registration/confirmation; Maintain separate, completely isolated email addresses for important functions; Use aliases or alternate spellings of your surname and make use of your middle name/s; Google multiple occupancy or serviced office addresses when a verifiable address is demanded; Make sure any supplied address matches the VPN country you are using; Consider setting up a mail-drop – near and/or far; Develop alternate signatures for forms, packages etc. and compartmentalize their use; Incorporating an LLC or using a business name can have privacy advantages; Make special efforts regarding the personal details held by your ISP and/or Telco; Consider posting well-wrapped cash or money orders for purchases.
Whenever supplying information online, assume it will be incorporated into a database forever. Assume that this will then be incorporated into a bigger search engine that merges multiple databases with all information about you. Assume that this will be available instantly to friend or foe, for free or a small fee.
 Sandisk SDSDQM-016G - ...
Buy New $4.25
(as of 01:55 UTC - Details)
Sandisk SDSDQM-016G - ...
Buy New $4.25
(as of 01:55 UTC - Details)
Data Backup Privacy
Special steps are needed for storing and transporting data privately, including through customs checkpoints, where your laptop could be seized:
Tiny micro SD cards are currently available up to at least 16 Gb. These can be tucked into a lapel, collar, hair clip etc. Or, an ideal, discreet and radiation proof solution would be inside a covert coin. Another option is to encrypt your data and upload it to the very useful, free Stashbox service, which will immediately return a web address to download it from later. Of course, there is always the old, "send it as an email attachment to yourself" method for smaller data backups.
Conclusion
Some might argue that actual criminals or terrorists could use these techniques to hide themselves. Possibly, but more likely they have other ways – like hacking in and controlling other people's computers, using other people's credit cards, and letting someone else take the blame. Either way, why should we all go into slavery, just to be "protected" from them?
Remember that governments are not omnipotent, though they would like to be. In reality, they are relatively few in number and there are many practical, economic and technological limitations. Also keep in mind sheer information overload – there can only be so many watchers.
But there is a real threat, particularly if you are targeted. In these perilous times I hope these privacy techniques will encourage you to speak out more freely and help you maintain more financial and personal security.
August 13, 2009





